The defacement is not stored and is only present when the URL has been crafted for that purpose. Only the defacement is present, so no other site content (such as branding) is rendered.By generating and tricking a user into visiting a malicious URL, an attacker can perform site defacement.
Similar Posts

Building Stronger Cybersecurity: James Beeson’s Vision for CCG
While real challenges vary by industry, there are several major challenges that are more universal. These include: I’ve known the founders of Cloud Communications since 2007 when we all completed our MBA studies…

From Guesswork to Clarity: Unlocking the Power of Insightful
If you care about productivity, accountability, and using your tools smartly, then this service is an excellent choice. These include: What is Insightful? A Quick Overview These timely notifications allow managers to step…
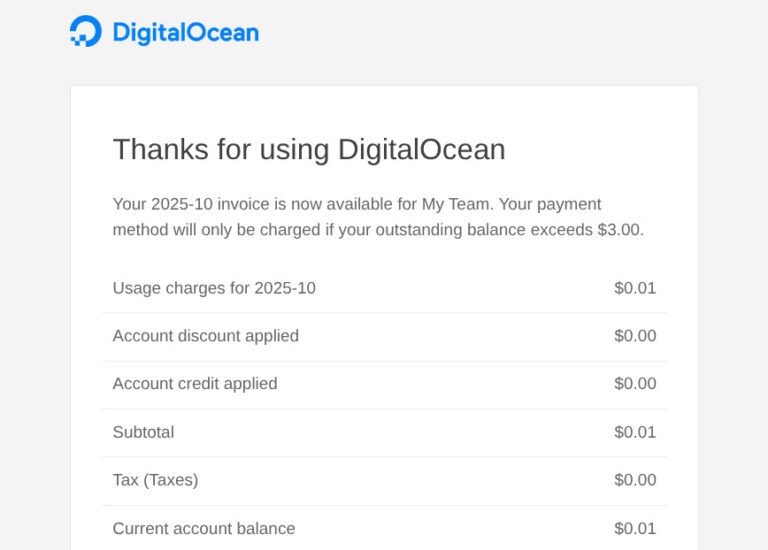
DigitalOcean is chasing me for $0.01: What it taught me about automation
There are three kinds of emails that can ruin a quiet Saturday: a security warning, an outage alert, and, apparently, a repeat reminder that you owe a cloud provider one cent, yes, $0.01….
Drupal Association blog: Showcasing Drupal Excellence: Refreshed Industry Pages and a Renewed Commitment
Regular review and updatesWe review these pages quarterly to ensure they showcase the best current work. However, if an exceptional case study is posted to Drupal.org between reviews, we may add it immediately….
Personalization at Scale: Why AI-Driven CDCs Are the Future of Customer Experience
At the same time, privacy regulations like GDPR and CCPA have added layers of operational complexity, demanding stricter governance and compliance measures. By Alfred Sin, Head of Personalization, Amperity The technology is ready….

My Drupal Core Contributions for week-ending August 23rd, 2024
I’ve been spending some time recently trying to get the Umami demo message from toolbar into the navigation module. I finished up last week with the HTML for the message being set in…
