


To get timely updates, follow us on LinkedIn, Twitter, Bluesky, and Facebook. You can also join us on Drupal Slack at #thedroptimes.We acknowledge that there are more stories to share. However, due to…

FinOps consulting has many advantages for companies trying to get the most out of cloud computing. The numerous and extensive benefits range from improved security and operational efficiency to cloud cost optimization and…

What trends are you seeing in the current M&A landscape, and how do you expect these trends to influence the demand for MSP services in the coming year? How does an MSP ensure…

This segmentation allows potential clients to easily identify which programs can best meet their fitness goals, ensuring a personalized experience. The site also features a dedicated FAQ page in the main menu. This…

A deep dive into language negotiation and path processing PHPStan Another adjustment we made was for the Redis in-memory cache. We increased the capacity and changed the max-memory purge policy to allkeys-lfu. That…
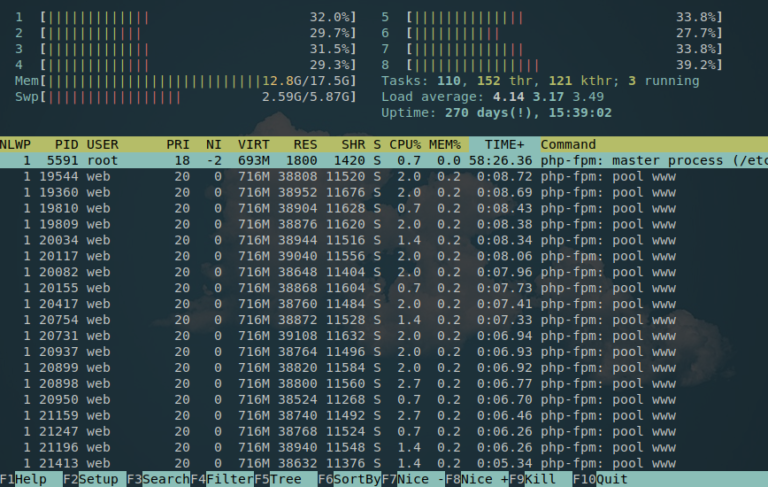
Some time ago, I received an email from a client experiencing slow performance issues with a LEMP (Linux, Nginx, MySQL, and PHP web server). During a full audit, I found that the server’s…