The defacement is not stored and is only present when the URL has been crafted for that purpose. Only the defacement is present, so no other site content (such as branding) is rendered.By generating and tricking a user into visiting a malicious URL, an attacker can perform site defacement.
Similar Posts

The Ethics of AI Detection: Consent, Transparency, and Trust
Ethical frameworks must keep pace with AI technology. Consent, transparency and trust shouldn’t serve as optional safeguards but rather be integrated as core values into daily practices. When regard for human values is…

Join the Drupal Starshot team as a track lead
However, we need many additional track leads to drive our remaining tracks to completion. We’re now accepting applications for track lead positions. Interested individuals and organizations can apply by completing our application form….
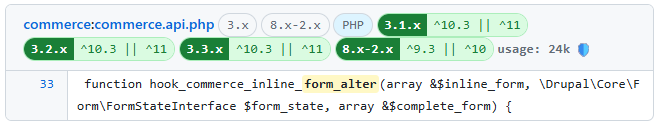
Très Bien Blog: Dig for gold in Drupal Contrib code
Instead of complaining I had the itch to fix it, that’s how Drupal contrib code search showed up. What are the differences? Use Drupal’s Gitlab search: kind of slow, a lot of noise…
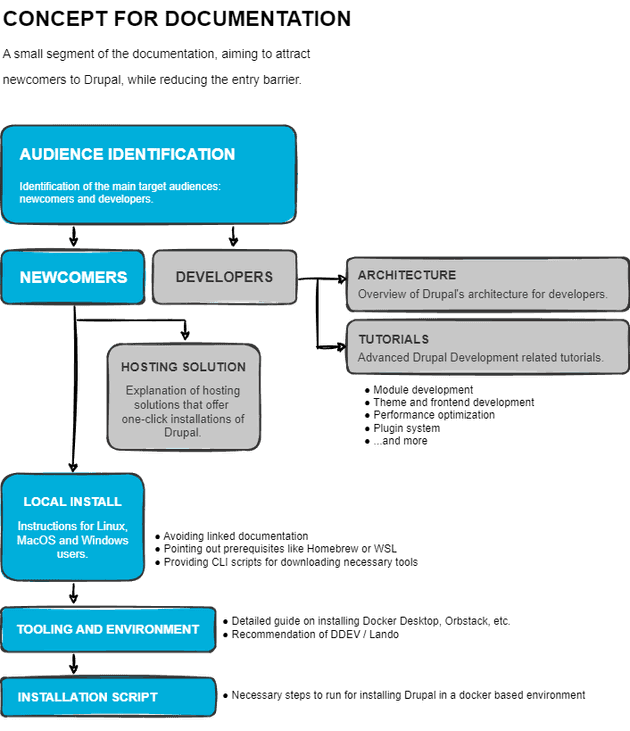
Simplifying Drupal Documentation | bPekker.dev
Of course, you could opt for the one-liner from the download page to create the Umami demo site, but if your goal is to truly understand Drupal, taking the shortcut might leave you…

CloudTweaks | Exploring Digital Sovereignty with Arman Borghem
Can you provide an example of a situation where lack of compliance led to significant consequences for a company? I’m not suggesting every organisation has to do everything on their own. In many…
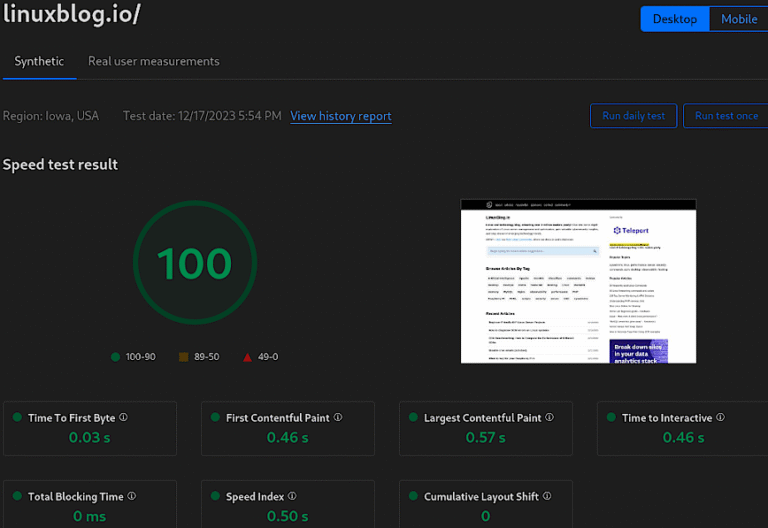
Recommended Cloudflare Performance and Security Settings (Guide)
Cloudflare is a great tool for website performance and security. They have a whole suite of tools to help with performance and security and are a staple in millions of DevOps professional’s toolbox….
