10 Linux Download Managers That Actually Work in 2026
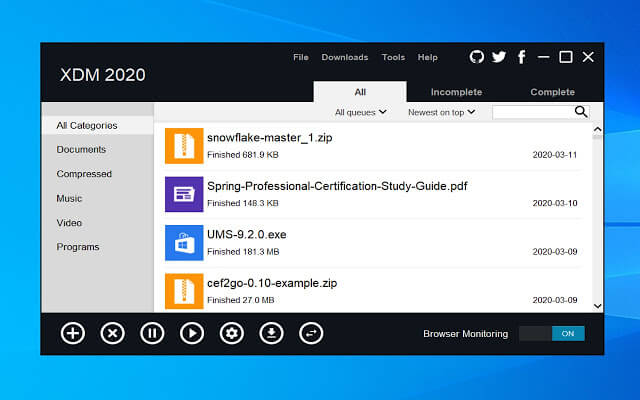
One thing many people miss after switching from Windows to Linux is a good download manager. Tools like Internet Download Manager (IDM) and Download Accelerator Plus are popular on Windows, but they aren’t…