In short, securing access for the modern enterprise has become, to put it bluntly, a mess. With a multitude of users and accounts spread across a variety of environments and systems – including both internal ones and those managed by third parties – businesses can simply no longer count on traditional security solutions to ensure that everyone (and everything) can do what they need to do, when they need to do it, and no more.
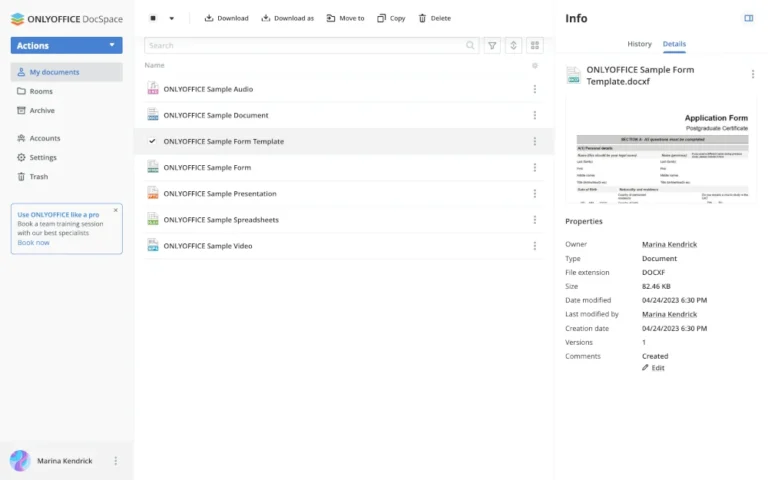
Of course, identity management tooling has evolved since the pre-cloud era. Businesses that manage human and machine access in complex environments can use systems like the Identity and Access Management (IAM) frameworks in public clouds. Similarly, Secure Access Service Edge (SASE) tools can help manage enterprise non-privileged user access to SaaS apps.
By Amol Kabe
How cloud computing changed security
Until about a decade ago, the typical organization had a clear perimeter. Based mainly on network location, it was easy to determine who or what was inside and who or what resided outside. This was primarily because most applications and data ran on systems that could be neatly segmented into zones of trust using traditional network firewalls. Plus, most users connected from fixed locations (like a corporate campus), so network location strongly correlated with trusted users or machines.
Identity firewalls integrate with platform-specific privilege management frameworks (such as the various IAM tooling of each public cloud). They provide a centralized vantage point for managing who can do what and when , across all the environments and systems a business relies on.
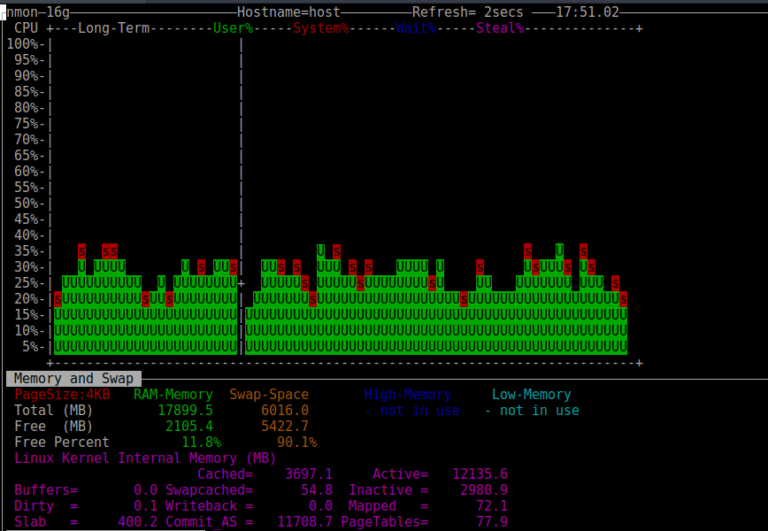
In this new world, inspecting packets between network boundaries does not work. For example, a database admin’s “DROP table” command can be fatal to a modern enterprise, and the network firewall cannot do anything about it.
And then, to top it all off, there are fundamentally new types of users to contend with – including not just machine users, but also AI agents, which also need authentication and authorization to ensure compliance and mitigate security risks.
By filling a gaping hole in modern security systems, identity firewalls allow businesses to minimize security and compliance risks linked to over-privileged users. At the same time, the ability to assign privileges seamlessly on an as-needed basis means that users don’t get locked out of resources they need to access. Just as next-generation firewalls enable secure network connectivity without disrupting workflows, identity firewalls control who can do what and when without getting in the way of what users need to do.
Plus, each of these components has its own consoles – whether SaaS or on-premises – for administrators.
The boundary has shifted. It used to be between networks. Now it’s between identities, systems and the actions they want to take.
IAM is not enough
A next-generation firewall allows businesses to define a flexible virtual network perimeter to help secure network access in IT estates, including an array of environments. However, in a world where identity is the new perimeter, an identity firewall controls privileged access from users, machines and agents across the entire IT estate.
The bottom line: Security needs have changed after the pivot to cloud-based, perimeterless environments. The way businesses manage security needs to change, too, with help from identity firewalls.
- Siloed tooling: IAM frameworks are specific to each public cloud, making it challenging to manage users and privileges centrally.
- Lack of dynamism: Most cloud IAM solutions lack native support for automated privilege changes or just-in-time access rights. In other words, they’re static.
- Focus on non-privileged users: Some cloud-centric identity management tools, like SASE solutions, focus on managing access for non-privileged users. However, they lack the granularity to grant specific configurations of privileges (like read and write access without delete permissions) on a user-by-user basis.
- Spotty coverage: Although many modern platforms feature some type of IAM or similar tooling, there are exceptions. A prime example is many of the agentic AI frameworks, which may gain built-in identity controls over time, but which generally do an inferior job of providing native identity management at present.
This is not to say that no one should use IAM, SASE or similar identity and privilege management solutions. On the contrary, these are important parts of a modern security strategy. But they’re insufficient to provide a holistic, granular, and dynamic approach to managing users and their privileges.
Enter the identity firewall.
This means that identity firewalls are a solution that both CISOs and end-users can love. They keep the business secure while enabling a seamless experience for employees and customers. As a bonus, they make life easier for IT and security teams, too, who no longer have to worry about manually configuring privileges across disparate systems or that an over-privileged account might slip through the cracks.
This is where identity firewalls come in. An identity firewall is a tool that continuously assesses the privileges of each principal – whether human, machine or agent – then grants or revokes permissions as needed. Identity firewalls inspect every privileged action between identity zones and decide whether to allow or deny based on policy.
Addressing this challenge requires a new approach to security – one rooted in a type of solution I like to call identity firewalls. Keep reading for a dive into what identity firewalls do and why they’ve become essential to security and compliance in the modern era.
SaaS apps add another layer of complication from a security perspective. They are hosted on someone else’s infrastructure, but they contain your corporation’s most sensitive information.
This new model has given rise not just to new approaches to network management (in the form of solutions like next-generation firewalls), but also new challenges in controlling the risk that arises from privileged access. When applications, data and users sprawl across multiple clouds and platforms, it becomes impossible to define simple boundaries between insiders and outsiders – to say nothing of assigning granular access rights to admins on an as-needed basis.
Instead, in this distributed world, organizations must enforce boundaries between identity domains and the commands flowing between those domains.
A solution CISOs and users alike can love
Many IT professionals now recognize that rigid network perimeters have disappeared in the cloud era. When users and the resources they access are dispersed across the internet, fixed boundaries no longer exist.
This increases the risk of insider threats – not just from rogue administrators but also from credential theft – which can lead to damage if privileged access to critical systems falls into the wrong hands. At the same time, companies face pressure to optimize the employee experience by avoiding disruptions, like cumbersome login processes, that may impact productivity or create friction for users.
This all changed with the shift to cloud-centric architectures. Today, the typical business has workloads spanning a diverse set of on-prem, private cloud, and public cloud environments. This makes it impossible to establish a fixed network perimeter, or to control who has access to what, based on the network alone.
These tools are certainly part of the solution for meeting modern security challenges. But they’re not enough on their own, for several reasons: